During a recent call with hospital executives, a CEO from a rural health care system shared his organization’s experience from a cybersecurity breach that occurred in 2020. The story was about a ransomware attack that took the hospital offline for two weeks and is still being restored now five months later. The increased frequency of cybersecurity breaches in health care, although clearly not good, provides much opportunity for sharing post breach “war stories.” In fact, the health care industry reports more breaches than any other.
He lamented that the organization had evolved in a way that resulted in accepting more risk than they had intended. Their last cybersecurity assessment was performed three years prior and many of the findings were either forgotten about or were no longer relevant because systems and processes had changed. Today, their IT staff, that was already overwhelmed, is struggling to act on the findings from seven different assessments performed by five different consultants. The pendulum has swung the other way.
Many organizations perform infrequent cybersecurity assessments while others perform many disparate assessments that are simply add-on work for existing IT staff that struggle to integrate cybersecurity into their overall IT projects and on-going operations. Today we are sharing a different approach that has proven to be more effective and more efficient than traditional assessments.
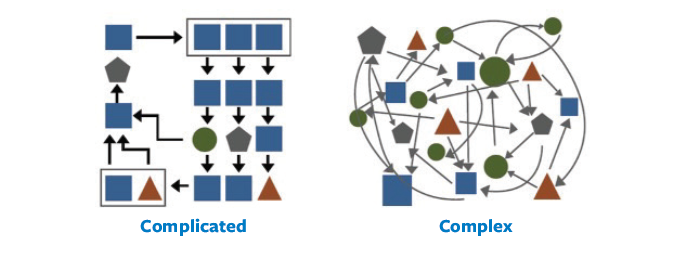
In 2017, author Rick Nason challenged the conventional wisdom that complicated and complex systems are the same. He differentiates that complicated systems are composed of known variables that behave in a predictable way. Mastering the logic of complicated systems has resulted in innovations and advancements such as satellite communications, microprocessors, and many of the IT systems that hospitals rely upon such as EMR systems and telehealth platforms. Complex systems are different in their complexity. They are composed of polymorphic variables that can interact and behave in unpredictable ways. Behavioral economics, cybersecurity, and cancer are three good examples of complex systems. This model also helps us understand how health care systems can spend more on cybersecurity each year (a complicated approach) while hackers win more than ever before (by exploiting increasingly complex systems) just like the ransomware attack referenced at the beginning of this article.
The Healthcare Security Operations Center (HSOC) is a cybersecurity capability created by health care for health care. Its core function is to protect the health care ecosystem from the threat of malicious hackers in a complex system. What started as a theory in 2017 has resulted in positive proof that frequent collaboration and sharing cybersecurity information before a breach helps prevent the exploitation of complex systems.
The first step in this approach is to advance from relying upon infrequent and disparate cybersecurity assessments to a continuous assessment model. A continuous assessment model is similar in that it informs specific controls such as NIST and HIPAA. It is different because it is workflow integrated, updated in near real time with objective metrics, and re-aligns tactics with strategy every month. One of the best parts of the model is that healthcare participants can share benchmark data and best practices anonymously or with attribution at their option. This continuous and collaborative approach offers a new and better way of assessing one’s cybersecurity posture. The old way of an annual or bi-annual assessment without real-time data has proven to be ineffective and puts an organization at greater risk of breach.

The HSOC provides collective cybersecurity defense for health care 24x7x365. While sharing war stories about breaches is a good start, it is much better to be part of a collective defense to prevent them from happening in the first place. The idea for the HSOC is rooted in the foundation for trusted sharing established by hospital associations for members to work on solving industry problems together. It is much more than just sharing of information and is more of sharing tactical ideas and best practices to protect all hospitals within the HSOC environment. Doing so in a way that it is a natural extension of both capacity and capability for the health systems existing IT and cybersecurity teams.
Consider how advancing to a continuous assessment approach and enacting collective cybersecurity could benefit your organization in 2021 and beyond. You may find, like many other health care leaders, that the otherwise elusive quest for efficiency and effectiveness from your cybersecurity technology investment can be realized.
This sponsored section is underwritten by THA Member Solutions. Cyberforce|Q is endorsed by the Texas Hospital Association. For more information, visit www.cyberforceq.com.